We Have the Technology: What happens when policy isn’t adapted to meet technological developments?
November 30, 2019
Technology is constantly changing – the past ten years have shown that. Humanity has gone from paper to computers, from traditional programming to adaptive AI, and from telephonic to instantaneous communication – all in the span of a century. Despite the dynamic nature of technology, the Northport-East Northport School District’s official technology policy is flawed, outdated, and lacks the necessary updates to keep it applicable to the current standard of technology.
The district’s technology policy centers around two Board of Education documents: Policy 4526, known as the “Computer Network for Education” policy, and its subset, Policy 4526.1, titled “Internet Safety.” While parts of these policies – such as the ‘Administration’ section of “Computer Network for Education” – are well thought out and were created to benefit students and educators, other parts of the policies are unjust to students, contradict district behavior, or are significantly outdated (the most recent revision of these policies was in 2010).
One example of these flawed policies is the “view.northport.k12.ny.us” subdomain designed for to enable students to access their school account desktop from home. Most people who have used this technology have probably never obtained “written permission from the Assistant Superintendent for Instruction and Administration” prior to using it. By failing to do this, most people who access their school accounts from home are in violation of the “Computer Network for Education” policy, which explicitly bans this practice without the aforementioned written permission.
The prohibited uses outlined under the same policy are even more interesting. Prohibited activities include “Revealing the personal address, telephone number or other personal information of oneself or another person” and “Wastefully using finite district resources.” This means that if a student were to tweet out personal information using the district’s Wi-Fi, they’d be in violation of the District’s IT policy. The second policy point, wasting district resources, is a vague prohibition that could forbid anything from running a computationally expensive program (like those used in AP Computer Science classes), to downloading a large file from the internet or network, and every other “wasteful” action in between. If you’ve ever used a personal USB drive or SD card on school computers, you’ve violated the part of Policy 4526 that prohibits “installing personal software or using personal disks on the District’s computers and/or network without the permission of the appropriate District official or employee.”
While some of these “rules” may seem funny, certain parts of these policies have serious consequences. One such policy point states that “Each individual in whose name an access account is issued is responsible at all times for its proper use.” This one line in the district’s “Computer Network for Education” policy allows the school to blame a student for the improper use of their network account, even if they are innocent of any wrongdoing. If a user with malicious intent logged on as another student in the district and committed a violation of district policy, this policy allows for the district to punish the student whose account was used instead of the person who actually committed the violation. While it is unlikely that a situation like this would ever occur, the fact that such a possibility exists in the district’s computer policy is indicative of the larger problems surrounding it.
The district’s internet and computer use policies are outdated and require revision in order to stay up to date with modern day digital technologies and concepts. As technology changes, the district must adapt to meet new technologies head on, with policies that are adaptable enough to apply to new technological developments, but outlined to protect student privacy and security online.
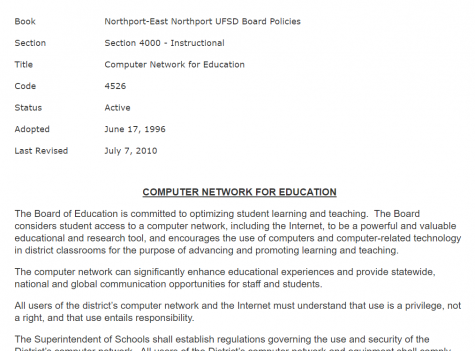
Figure 1 – A snapshot of the NENUFSD’s Policy 4526 taken on 11/15/19